Connecting ServiceNow
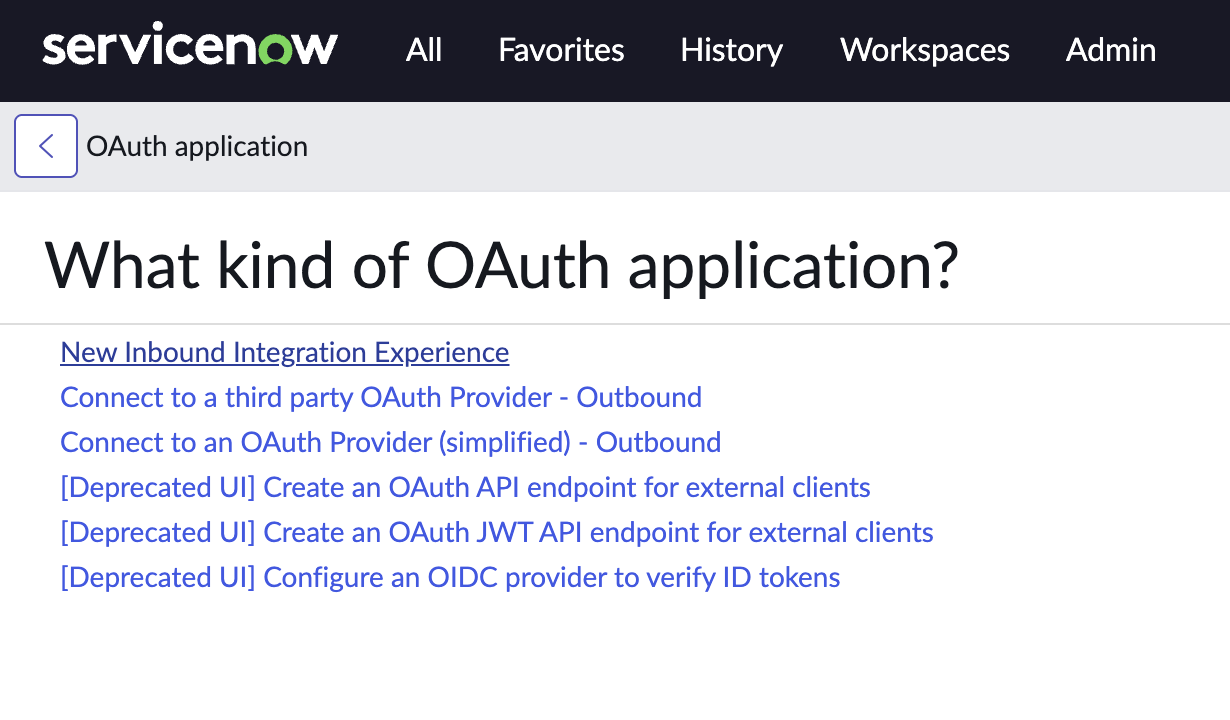
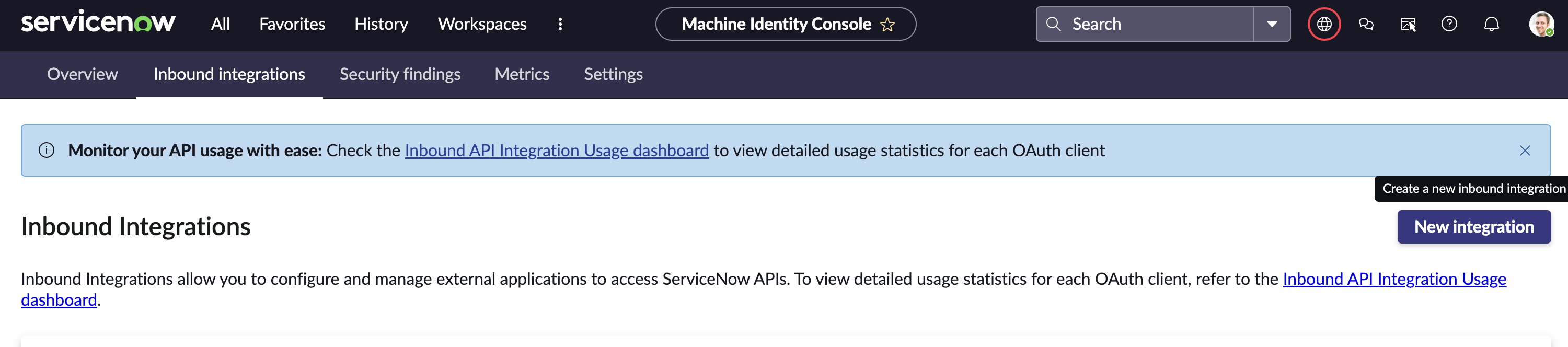
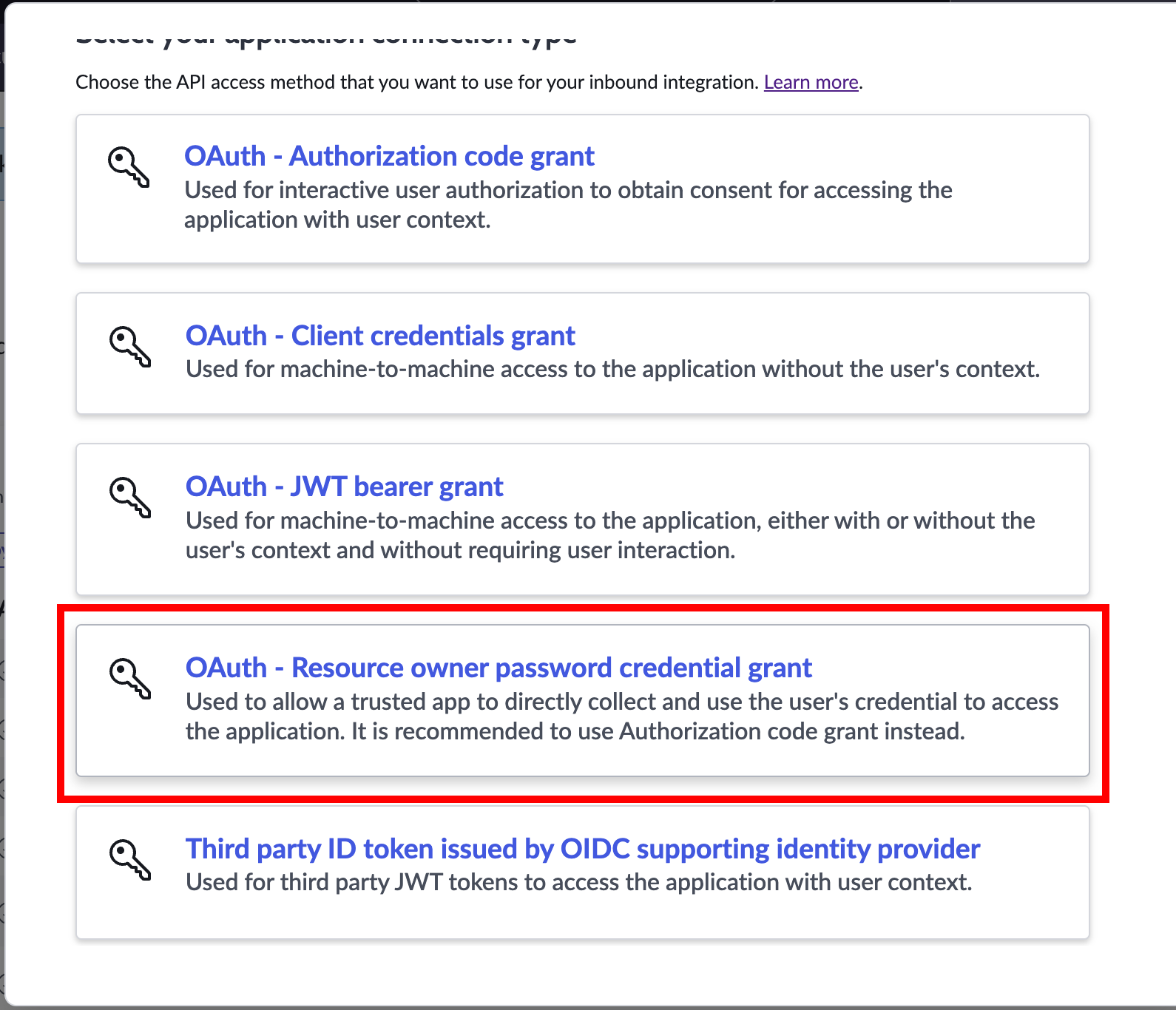
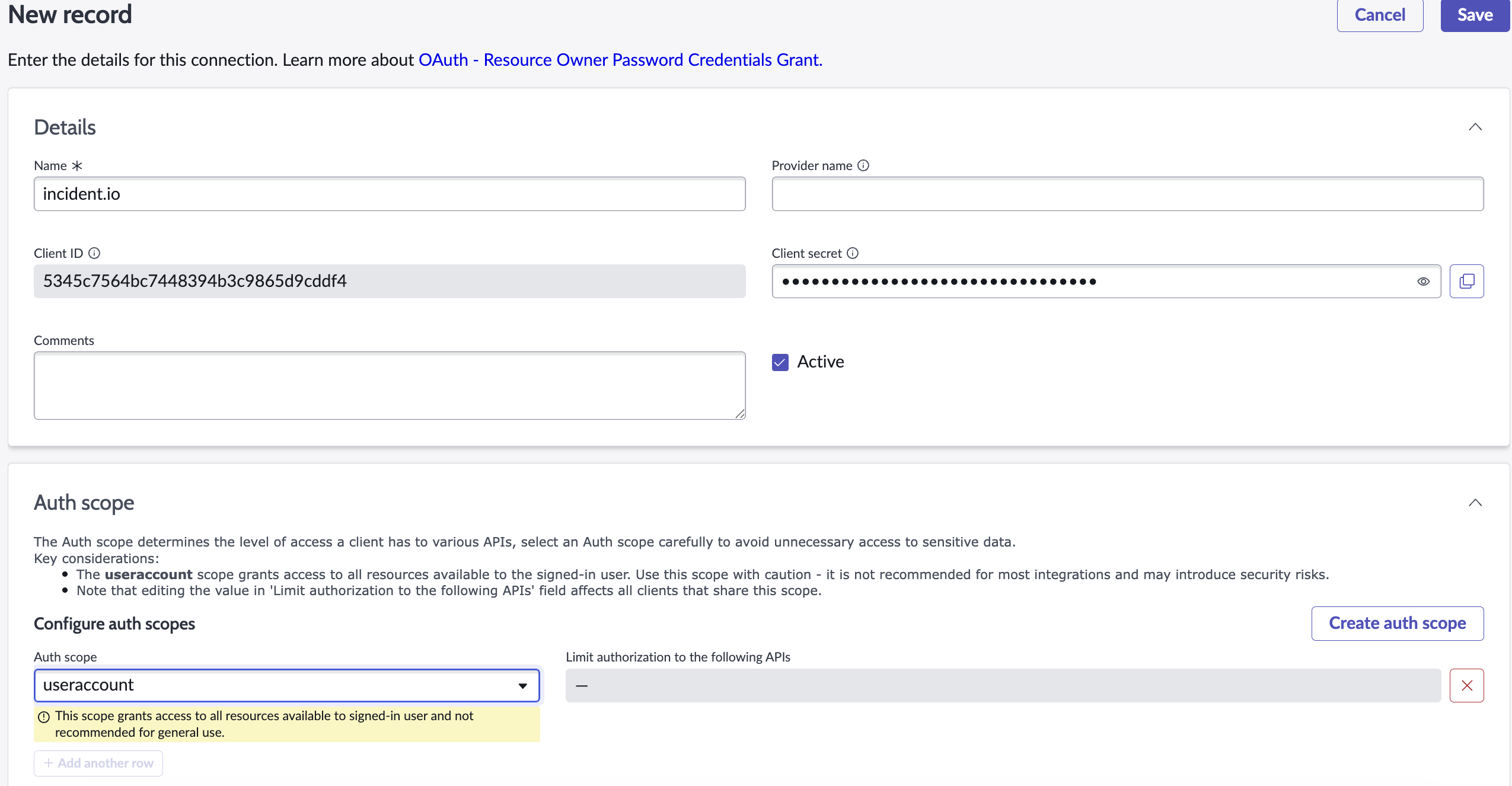
incident.io connects to ServiceNow using an OAuth app and Web Service user account. Let’s get started with the OAuth app.1. Create an OAuth App
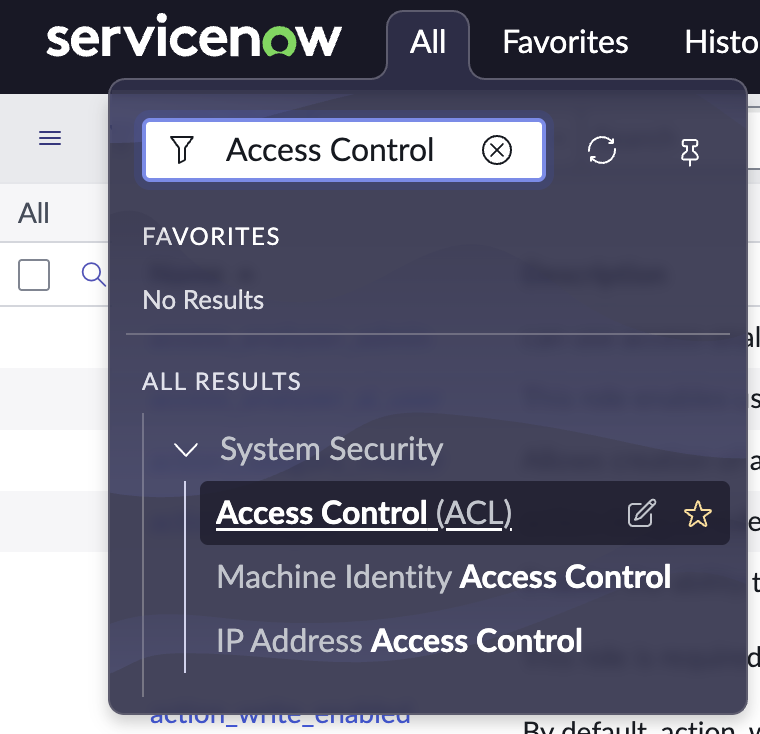
Log in to ServiceNow and search for “OAuth” in the filter navigation: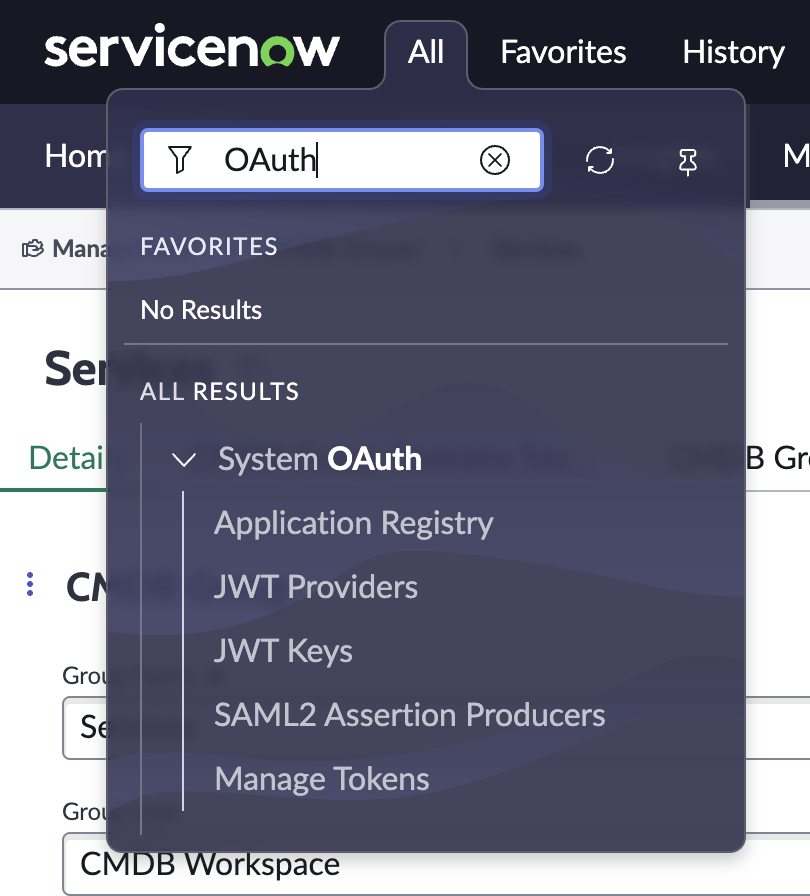
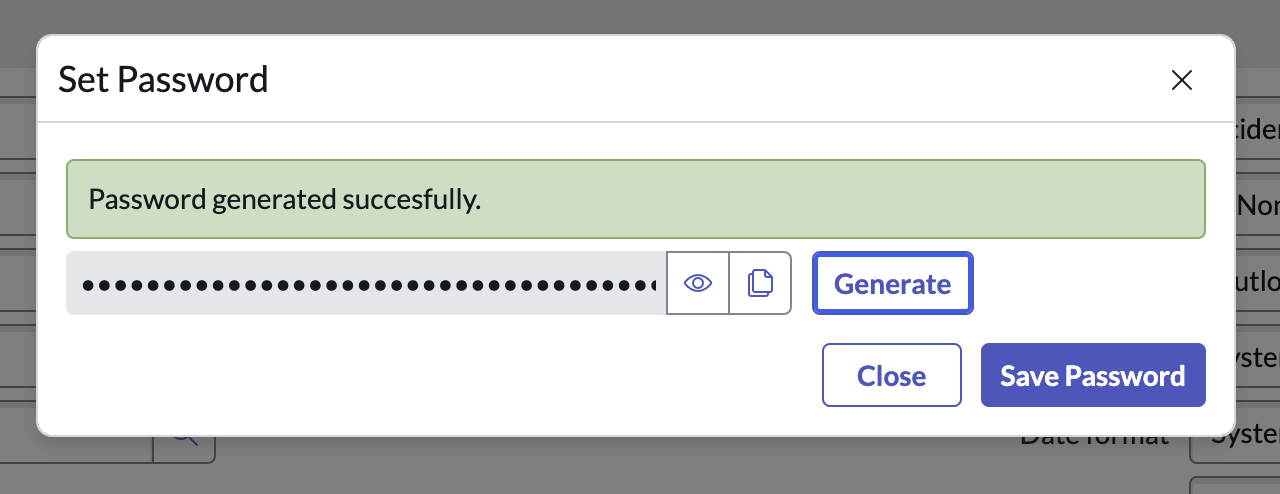
2. Create a Web Service Account
Any ServiceNow user account can be used so long as it has the relevant roles assigned. However, any actions taken by incident.io in ServiceNow will appear as being taken by this user account, so we strongly recommend creating a user for this purpose only.
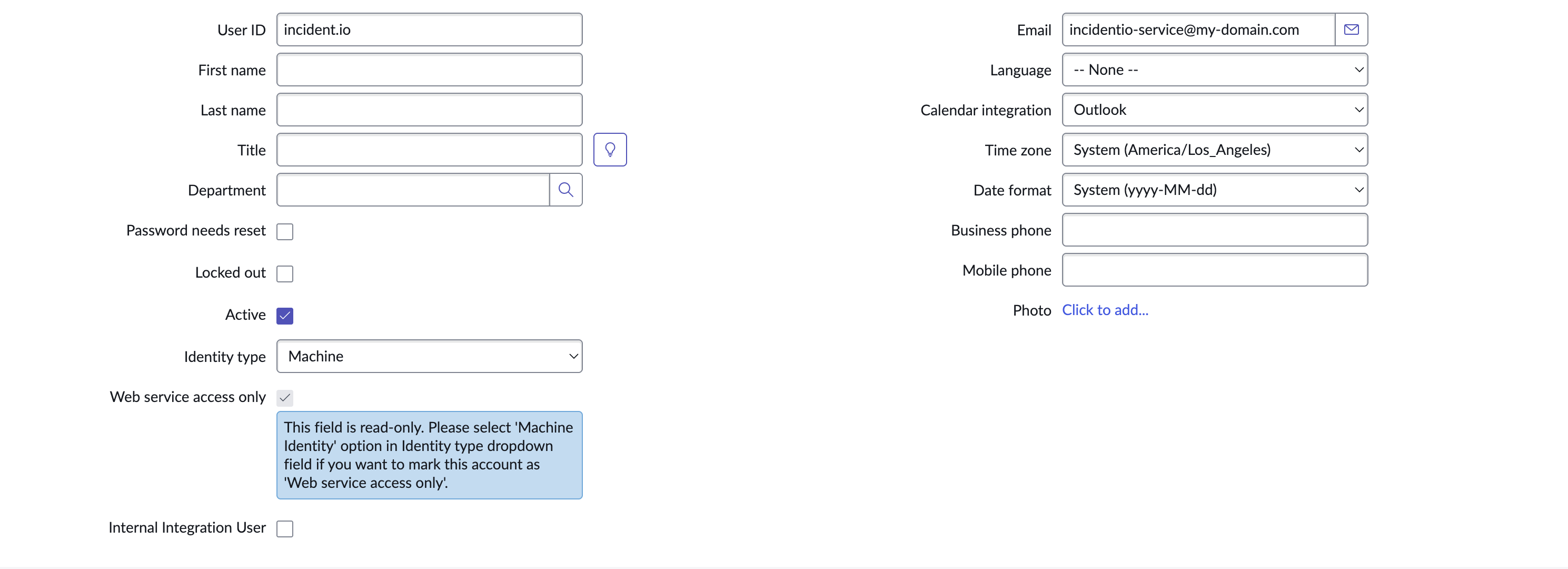
admin: allows us full access to your ServiceNow instance. This is the recommended approach, as it ensures all current and future features work without additional configuration.- If you don’t wish to grant the
adminrole, create the user without theadminrole and follow the granular permissions section below to create a custom role.
- If you don’t wish to grant the
3. Installing the integration
We’re now ready to install the ServiceNow integration in incident.io. Go to Settings → Integrations, and click on ServiceNow, then Connect.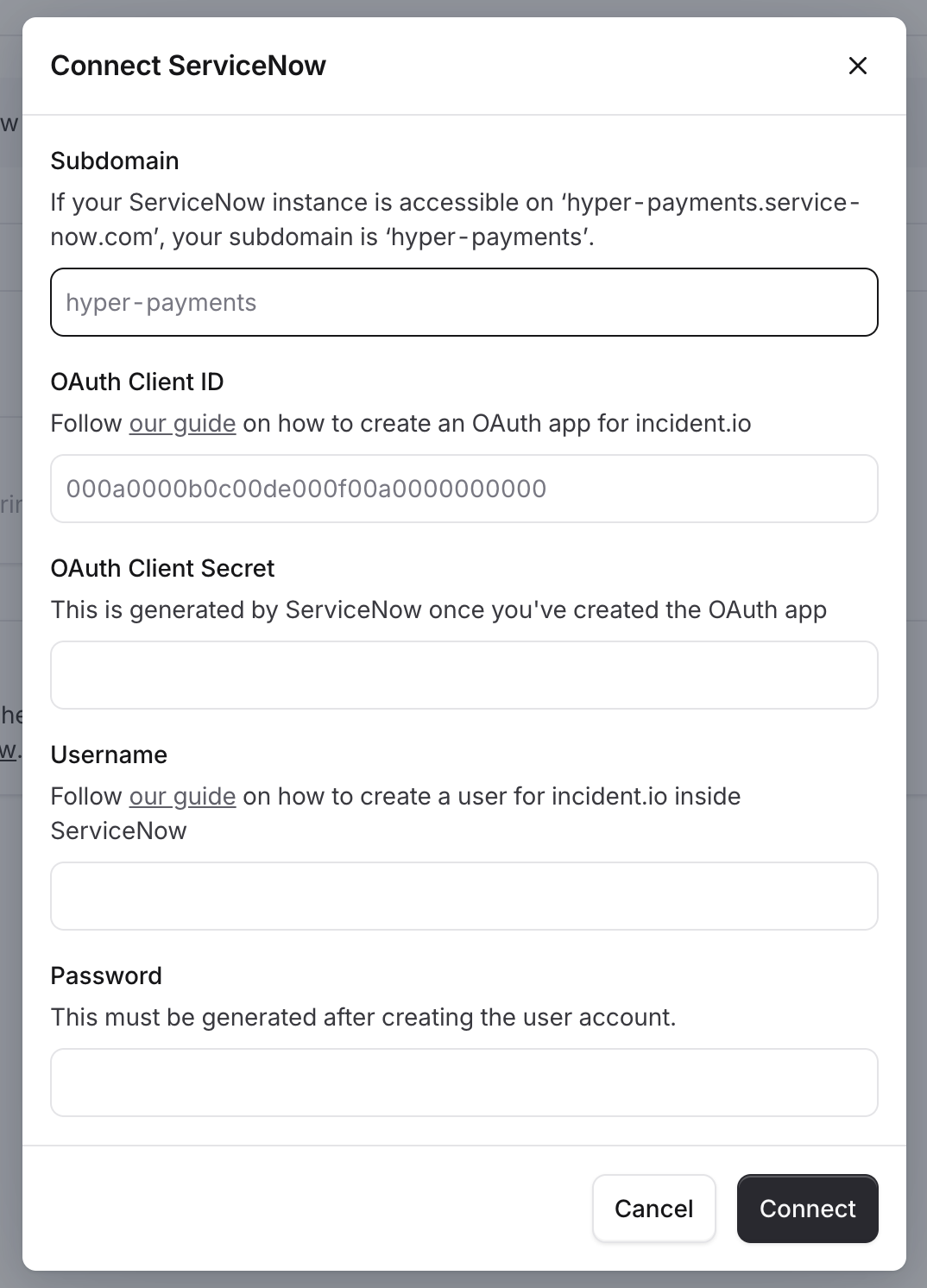
- Your subdomain is the part of the URL where you log in to ServiceNow. For example, if your ServiceNow instance is accessed at
hyper-payments.service-now.com, your subdomain ishyper-payments. - Your OAuth Client ID and OAuth Client Secret are the credentials you created in part 1 above.
- Your Username and Password are the credentials for the service account you created in part 2.
- Click Connect to verify your credentials and complete the connection
Granular Permissions
If you do not wish to grant theAdmin role, you can set-up a custom role and assign it to the service user.
Custom Role
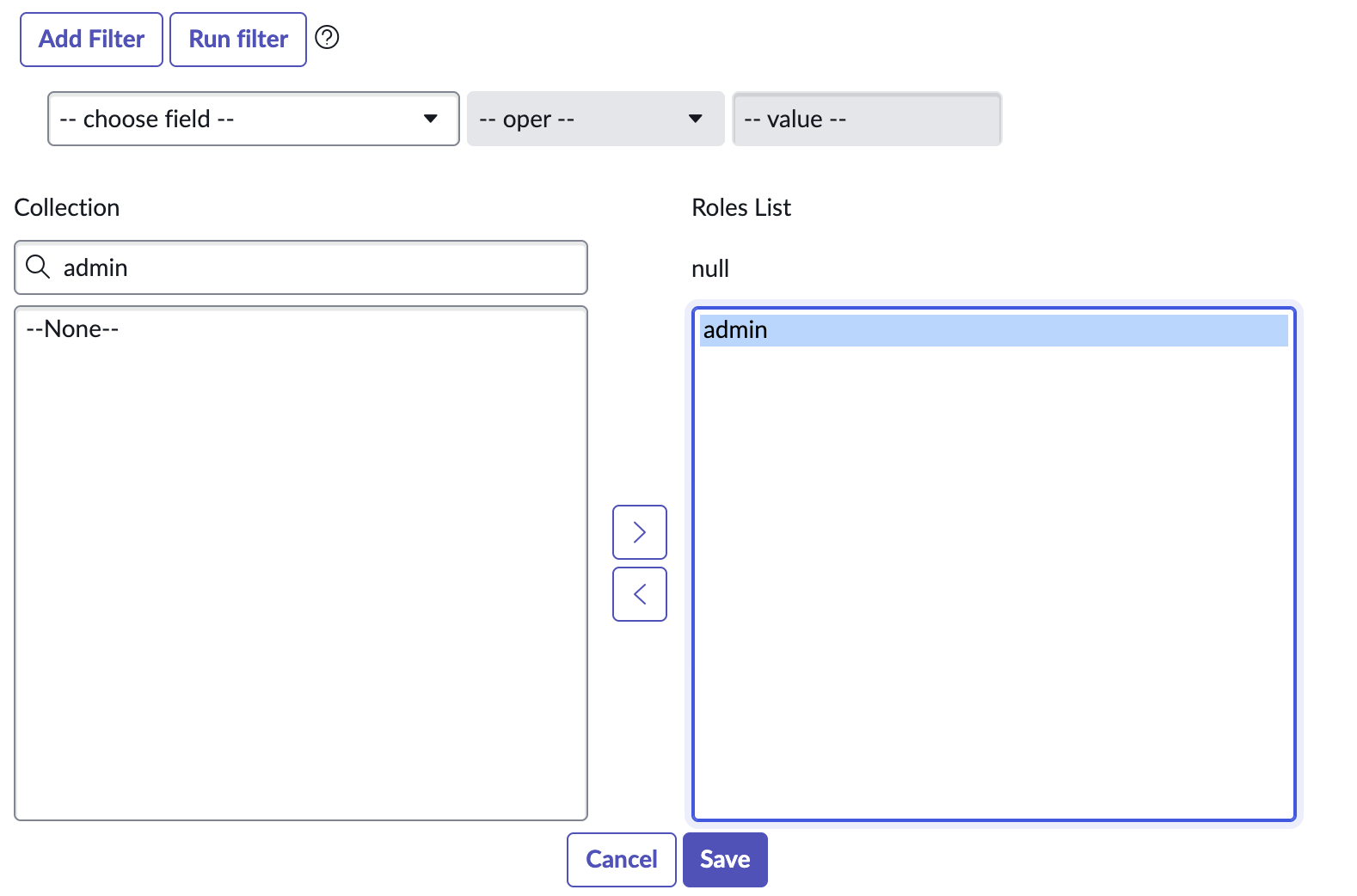
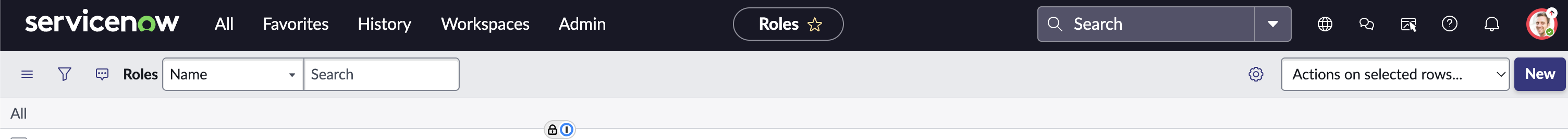
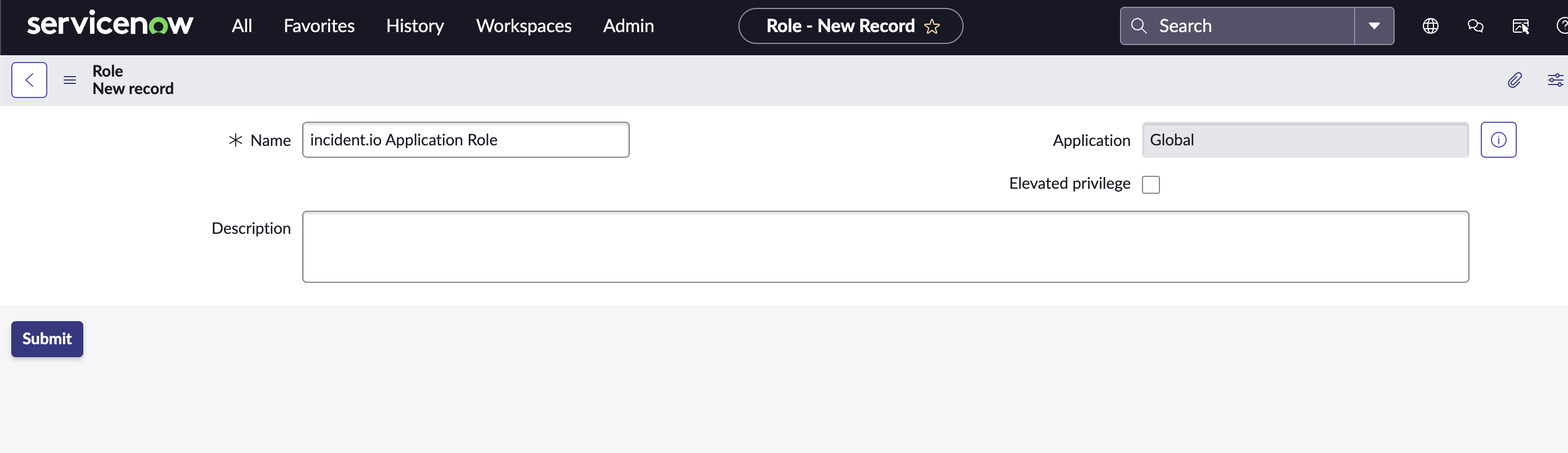
First, we need to create a new role for the service user. Search for ‘Roles’ and select the ‘Roles’ option under ‘Users and Groups’.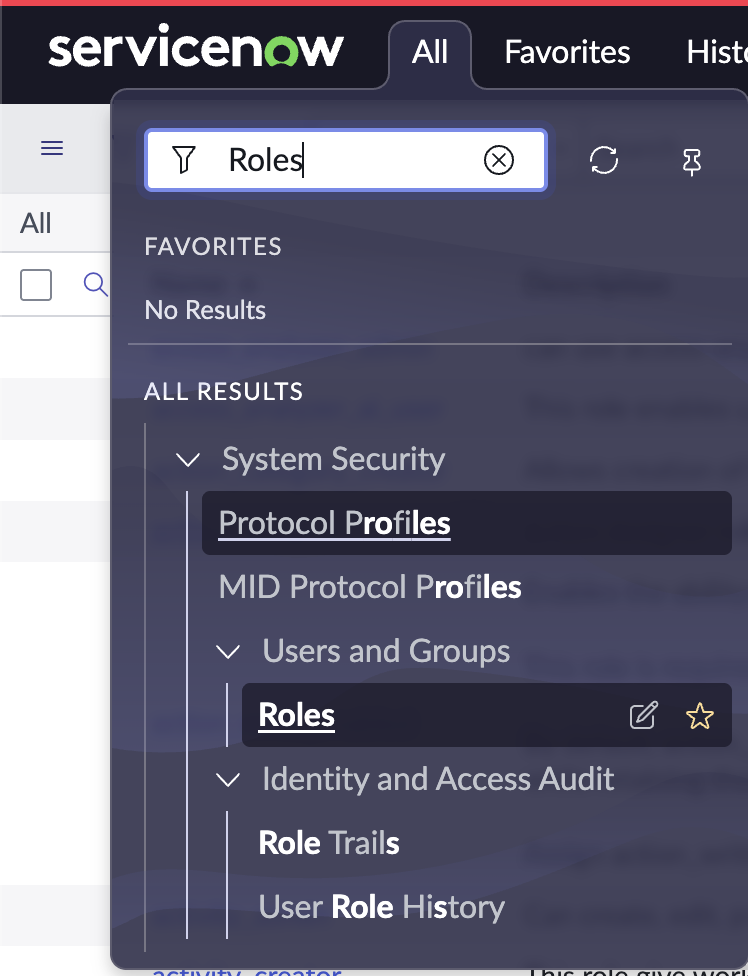
incident.io Application Role.
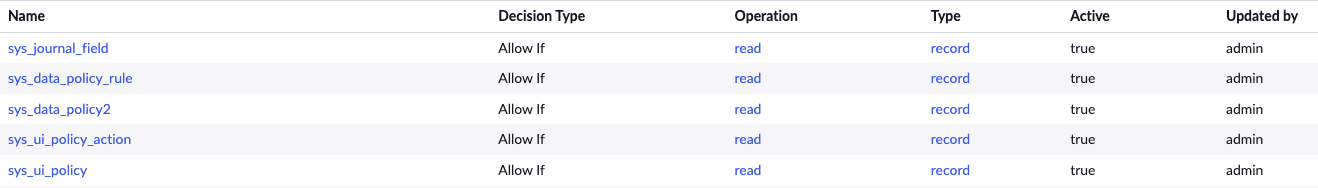
ACLs
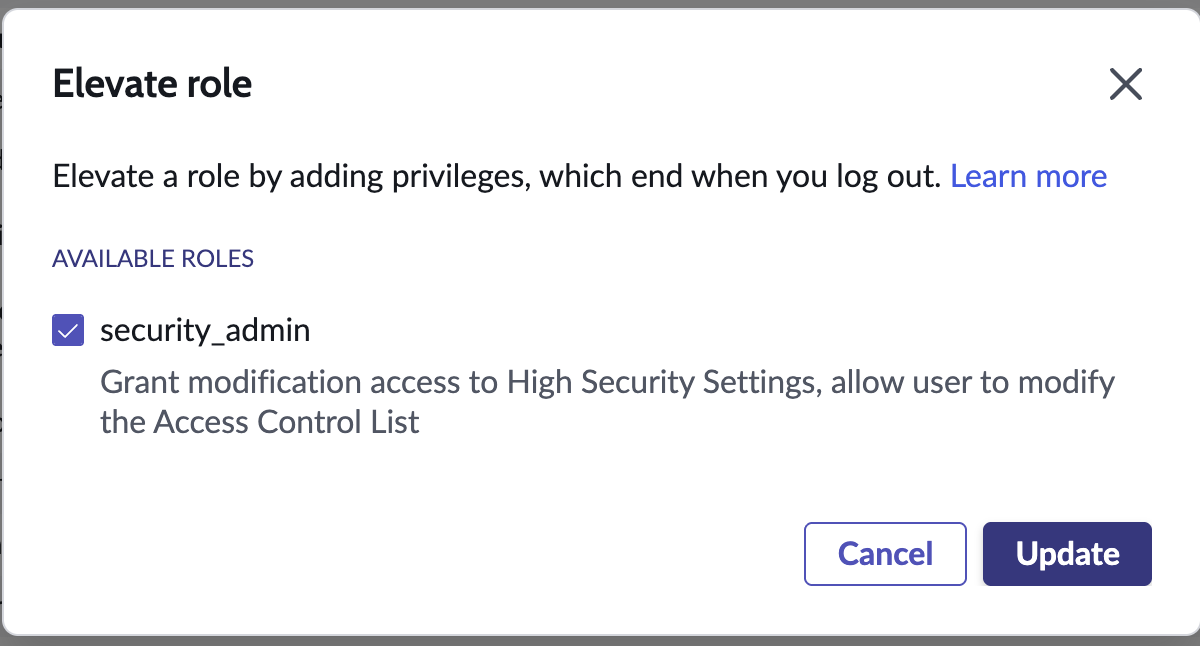
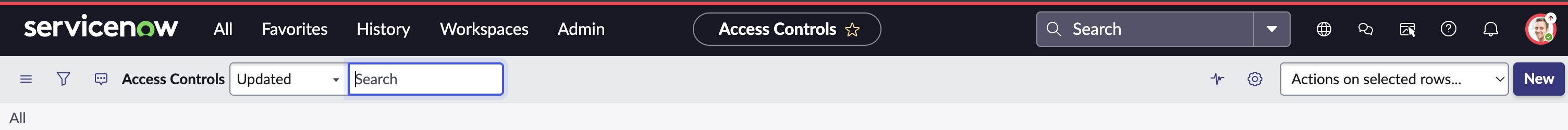
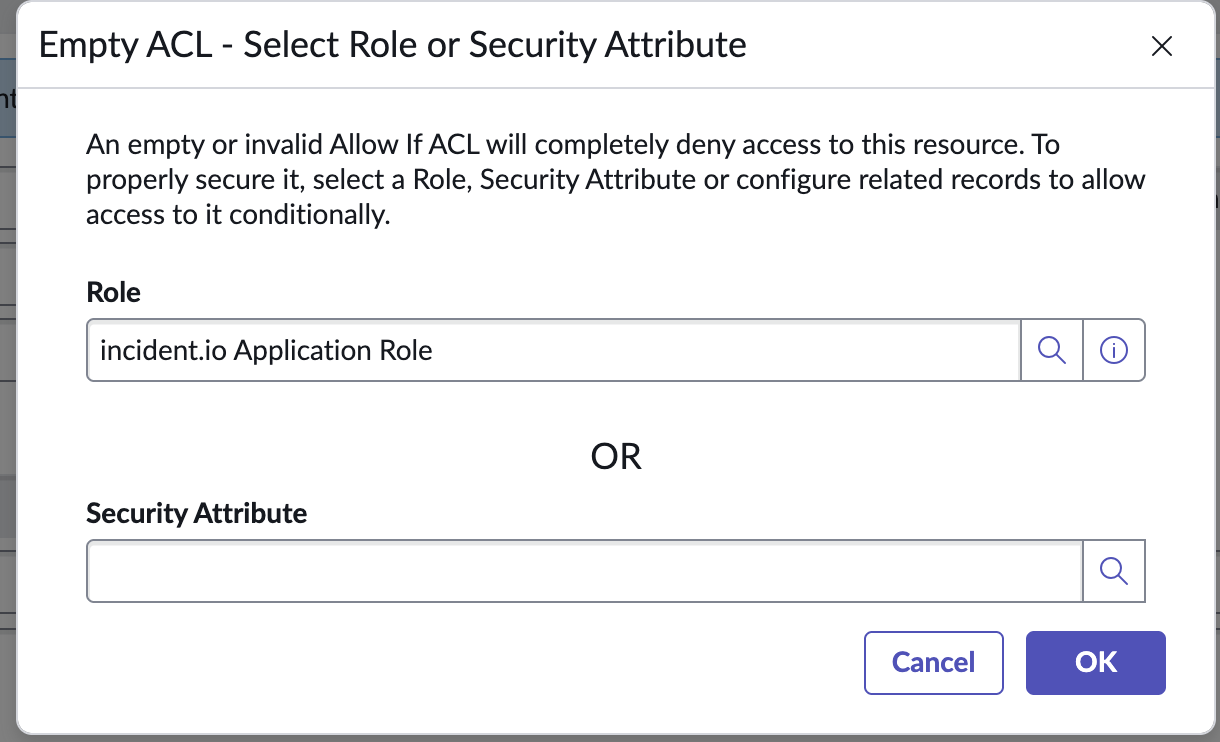
Next, we need to create new ACLs that grant read-only access to the data and UI policies. To add new ACLs, you first need to elevate your user to Security Admin. Click your profile icon and select ‘Elevate role’.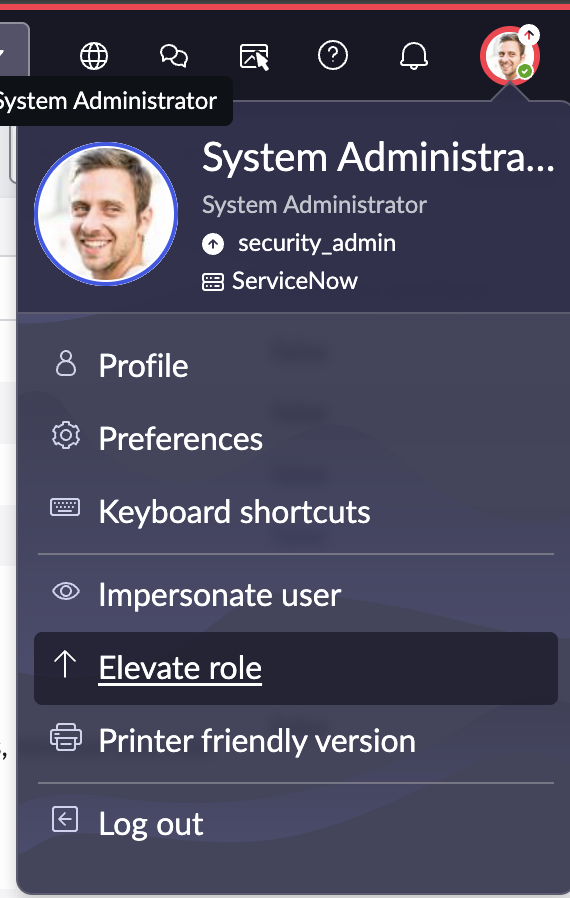
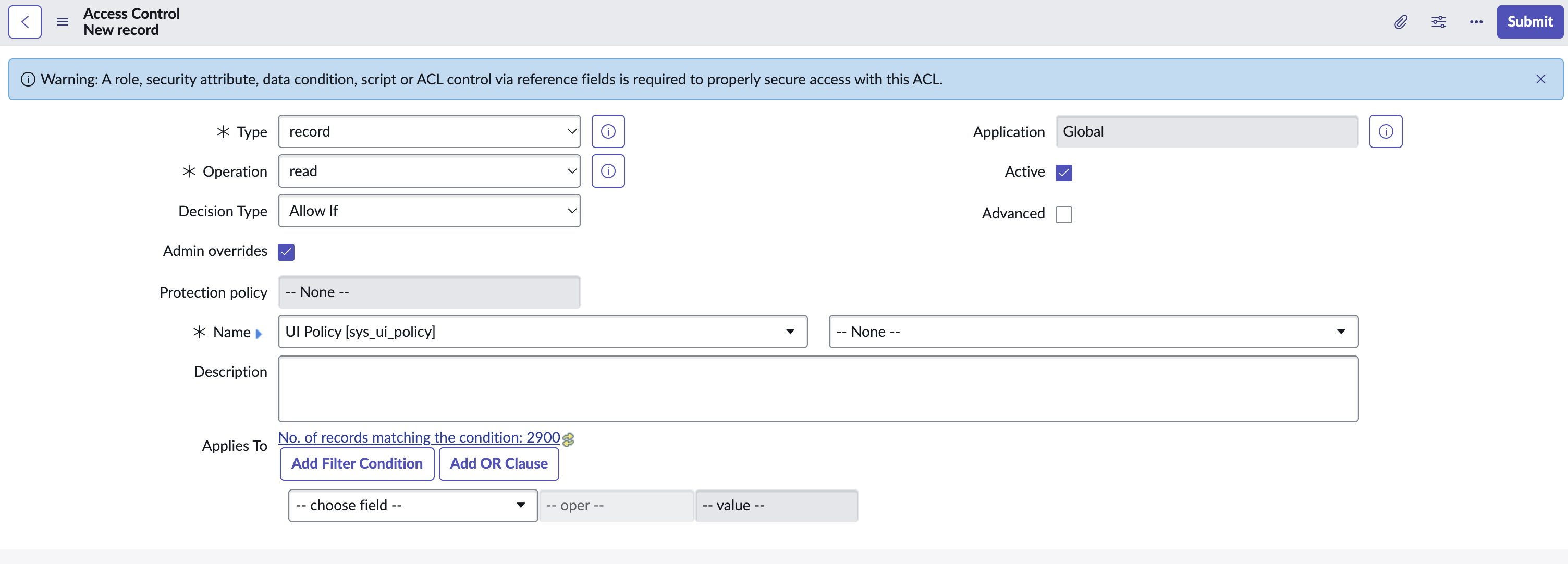
sys_ui_policysys_ui_policy_actionsys_data_policysys_data_policy_rulesys_journal_fieldtask
- Type:
record - Operation: Change from
createtoread - Application:
Global - Active: checked
- Decision Type:
Allow If - Admin overrides: checked
- Name: Type the table name in the first dropdown.
- Leave the second dropdown as
-- None --.
- Leave the second dropdown as
sys_ui_policysys_ui_policy_actionsys_data_policysys_data_policy_rulesys_journal_fieldtask
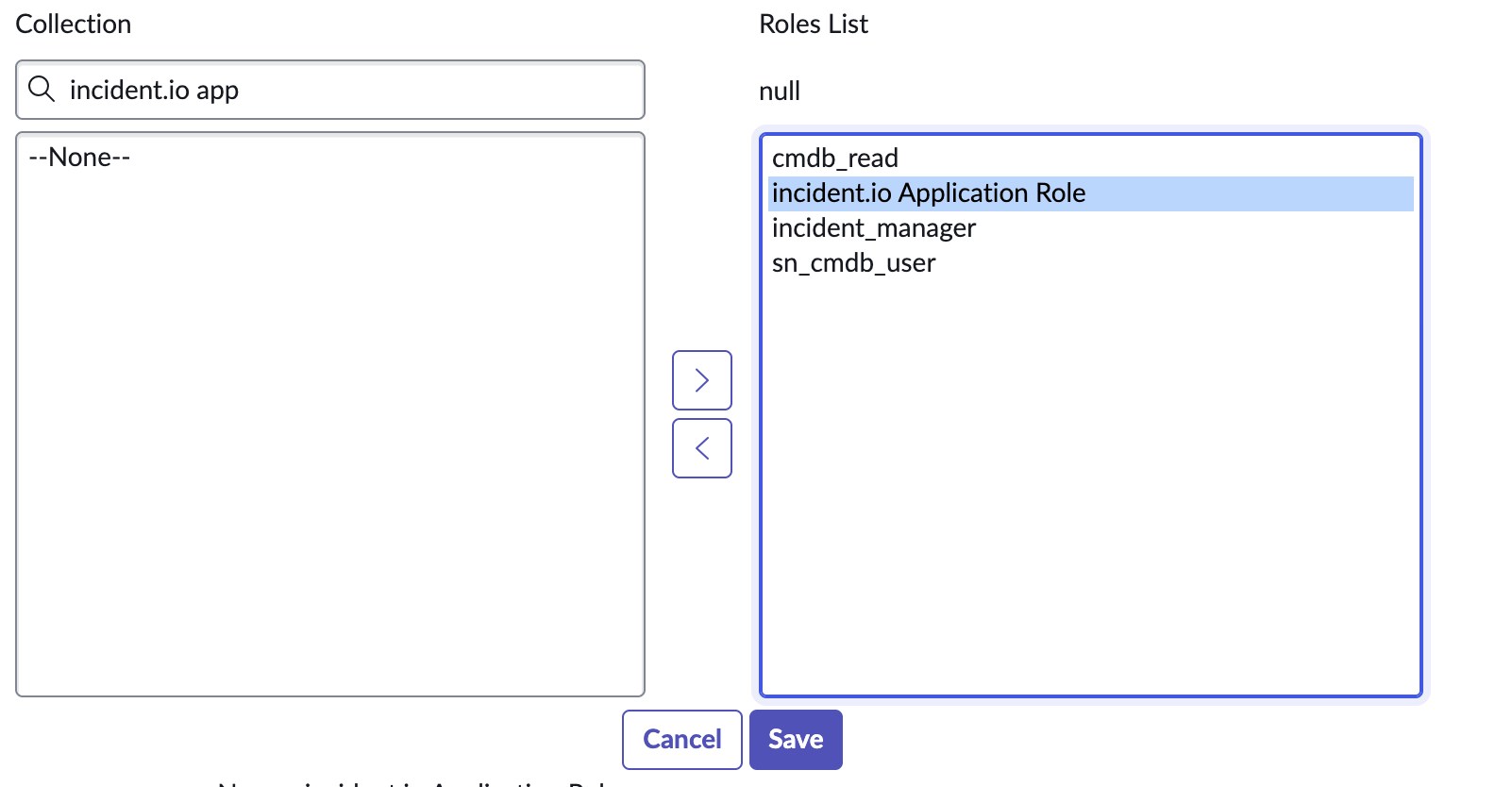
Assign Roles To The Service User
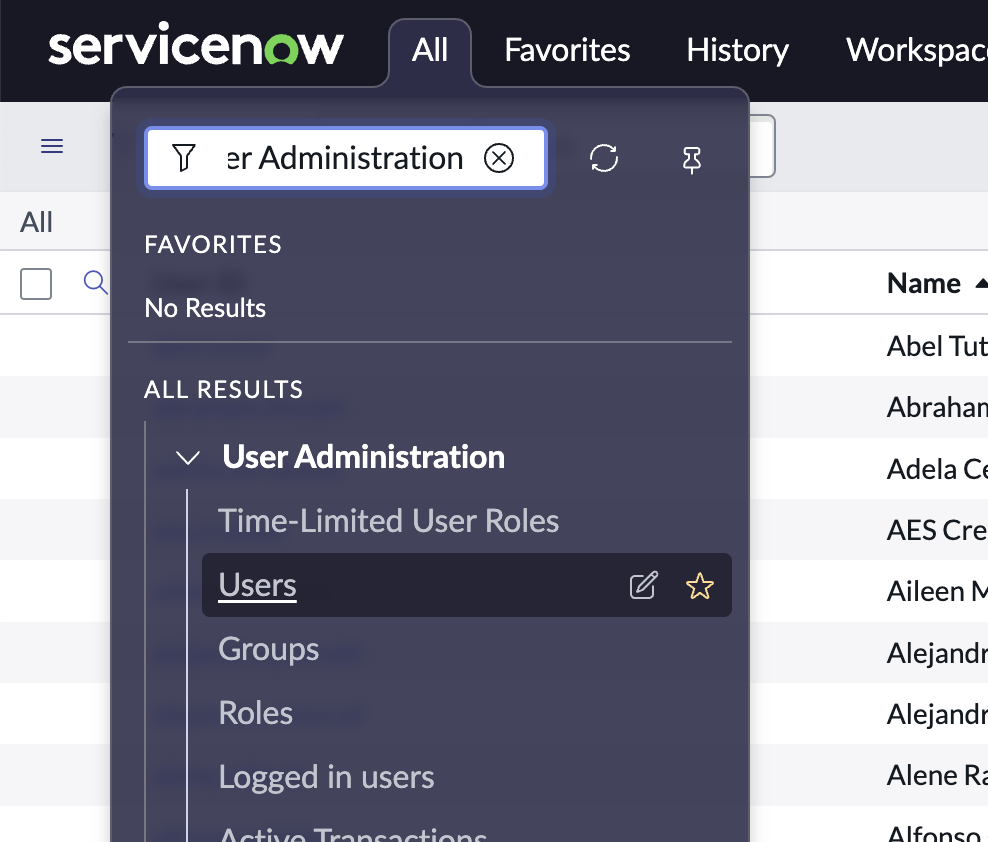
Now that we have the role and the ACLs, we need to add the required roles to our user. Search for ‘User Administration’ in the filter navigation: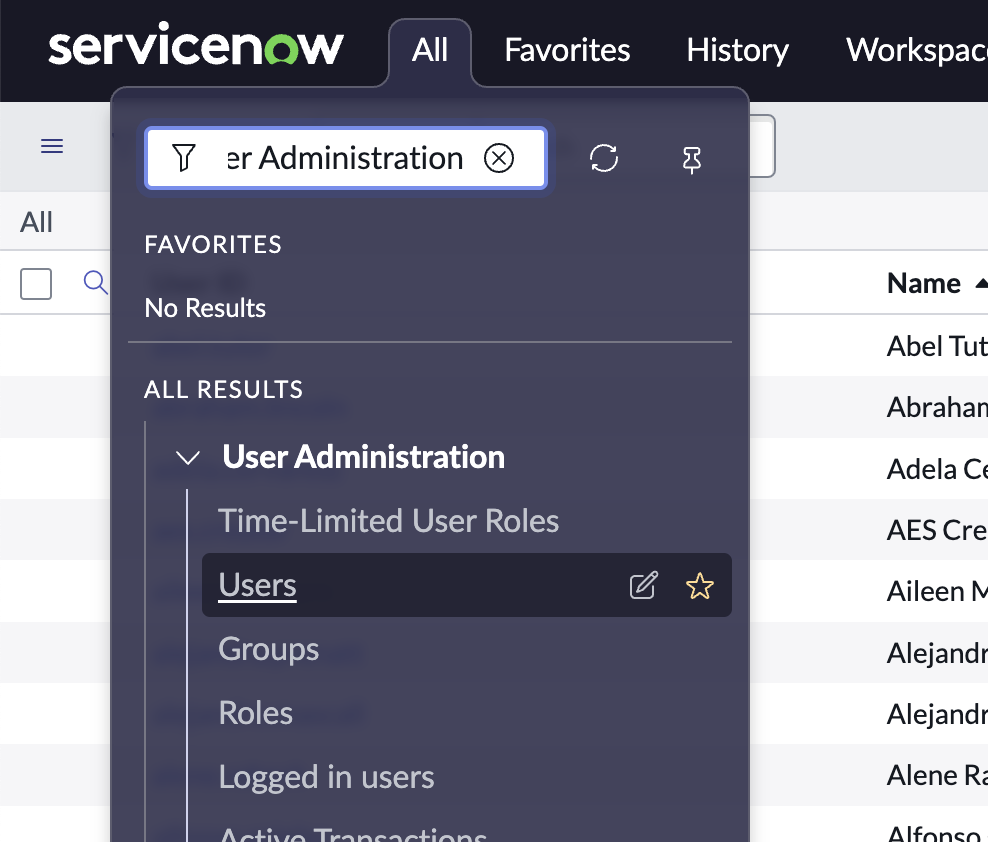
cmdb_read: allows us to read data from your Configuration Management Database.sn_cmdb_user: allows us to read information about users and groups in your ServiceNow account.incident_manager: allows us to sync incident data into ServiceNow incident records.incident.io Application Role: allows us access to UI and data policies, as well as work notes on incidents.