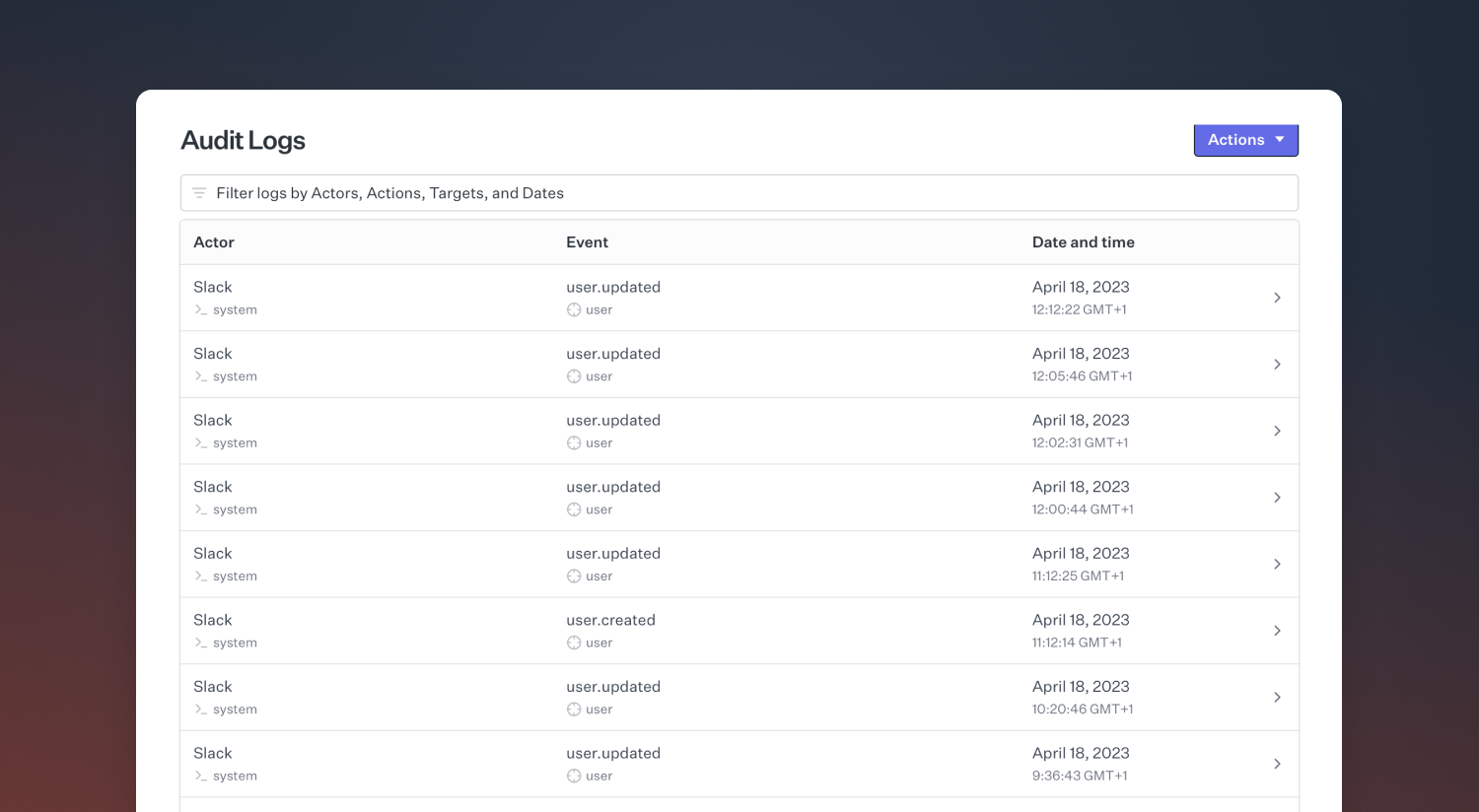
You must be an Owner or Admin to access audit logs. Entries are available from April 18, 2023 onwards.
What’s tracked
Audit logs capture configuration changes across incident.io, including:- Alert sources, routes, and escalation paths
- Schedule and on-call configuration changes
- User role assignments and permission updates
- Access grants to private incidents
- Workflow and automation changes
- Integration configurations
Viewing audit logs
Access audit logs at Settings → Security. From there you can:- View entries in a web interface, filterable by target, event type, actor, and date
- Export entries for a given time period to CSV
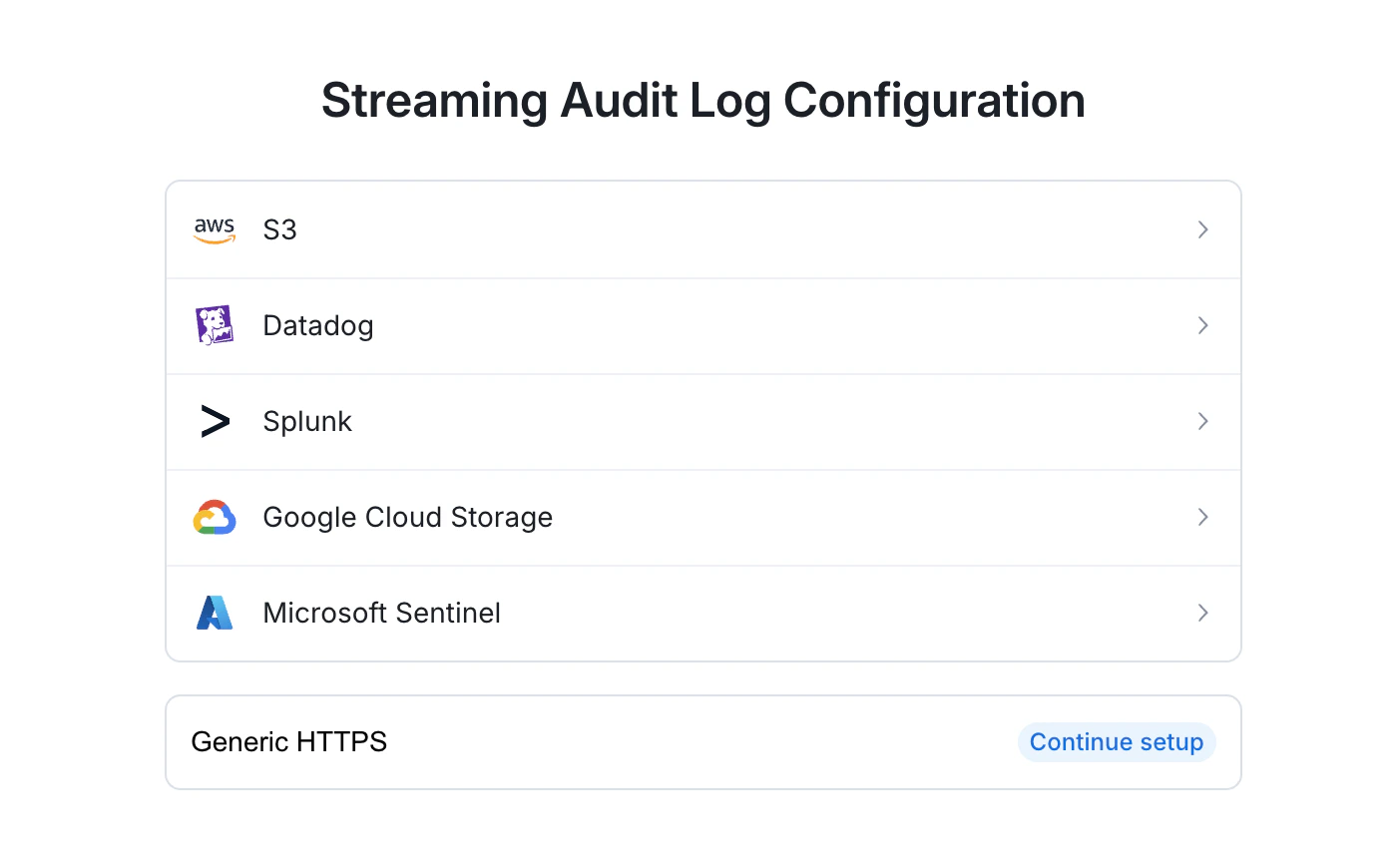
- Set up a log stream to a SIEM provider (e.g. Datadog, Splunk, or an Amazon S3 bucket)